-
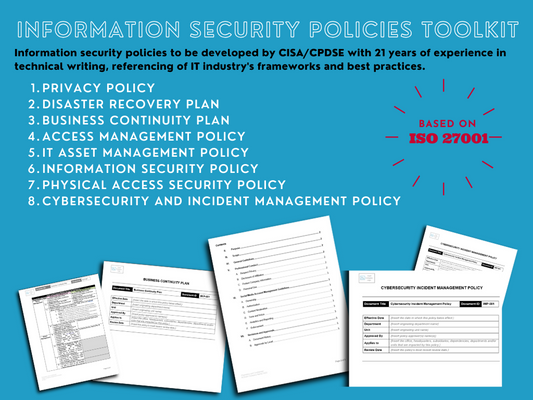
Information Security Policies Toolkit **Out-of the-Box/Editable** Templates
Regular price $39.99 USDRegular priceUnit price / per -
GRATIS - Guía rápida de implementación de AI
Regular price $0.00 USDRegular priceUnit price / per -
FREE AI Implementation Quick Guide
Regular price $0.00 USDRegular priceUnit price / per -
Password Management Policy Template
Regular price $7.99 USDRegular priceUnit price / per
Blog posts
View all-

Exploring the Correlation Between Four Pillars ...
In the universe of IT auditing, where the landscape constantly evolves and transforms, there exists a fundamental framework composed of four pillars: Risk Management, Compliance, Governance and Controls. These pillars...
Exploring the Correlation Between Four Pillars ...
In the universe of IT auditing, where the landscape constantly evolves and transforms, there exists a fundamental framework composed of four pillars: Risk Management, Compliance, Governance and Controls. These pillars...
-

The Critical Role of Information Technology Gen...
For years, most businesses have connected their operations to technology, and the pandemic accelerated this digital shift. The great significance of technology in business functions results in the need to...
The Critical Role of Information Technology Gen...
For years, most businesses have connected their operations to technology, and the pandemic accelerated this digital shift. The great significance of technology in business functions results in the need to...
-

The Vital Role of Security Policies and Risk As...
Information systems and the data they contain face a wide range of risks. Organizations rely on technology for their vital operations and activities, that’s why they need to be aware...
The Vital Role of Security Policies and Risk As...
Information systems and the data they contain face a wide range of risks. Organizations rely on technology for their vital operations and activities, that’s why they need to be aware...